Launch secure applications
Use built-in safeguards and proven infrastructure to control access, protect data, and deliver reliable business software
Use built-in safeguards and proven infrastructure to control access, protect data, and deliver reliable business software
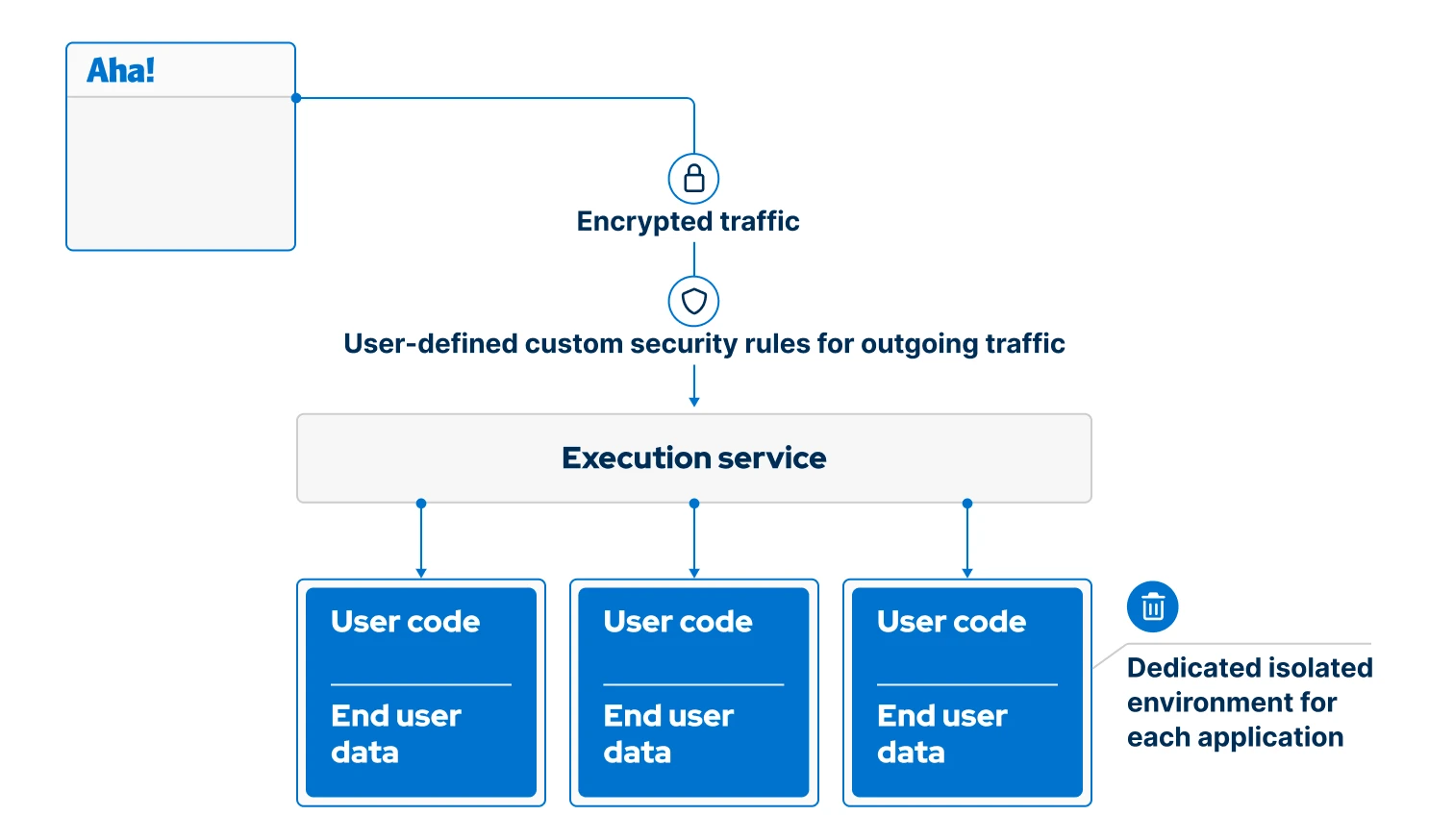
Do not let security be an afterthought. Aha! Builder puts strong controls in place from the moment you start building. The user interface is separated from the back end, limiting database access to a controlled server-side layer. Every request flows through this layer — and nothing runs without explicit authentication. This prevents common mistakes that could expose data or create insecure access paths.
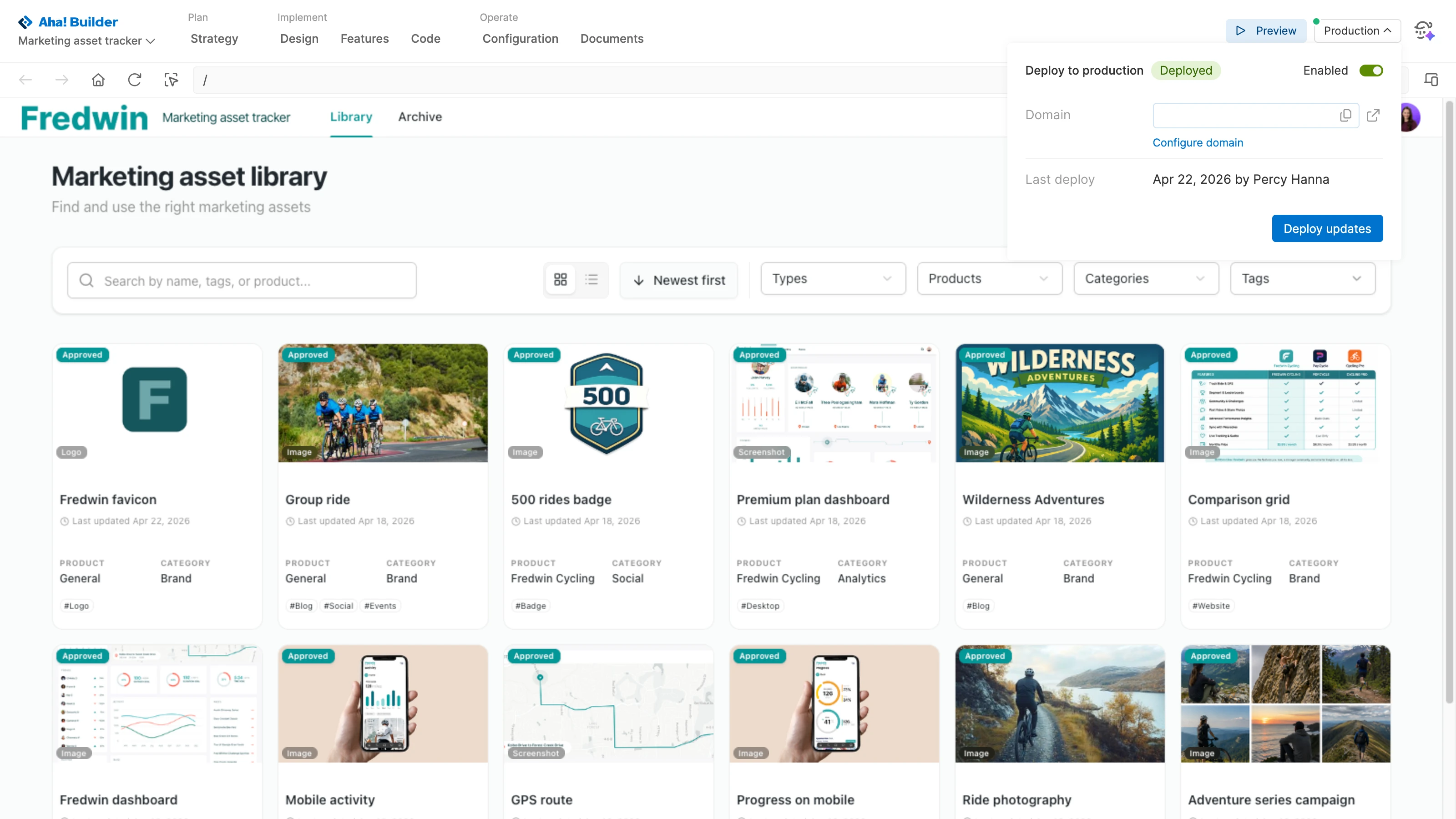
Keep development and production environments fully separate. Build and validate changes in preview mode before deploying to production. Each environment maintains its own database and authentication configuration — separating test activity from live usage. This gives the team an isolated way to iterate with Elle, the AI assistant, without impacting production data or users.
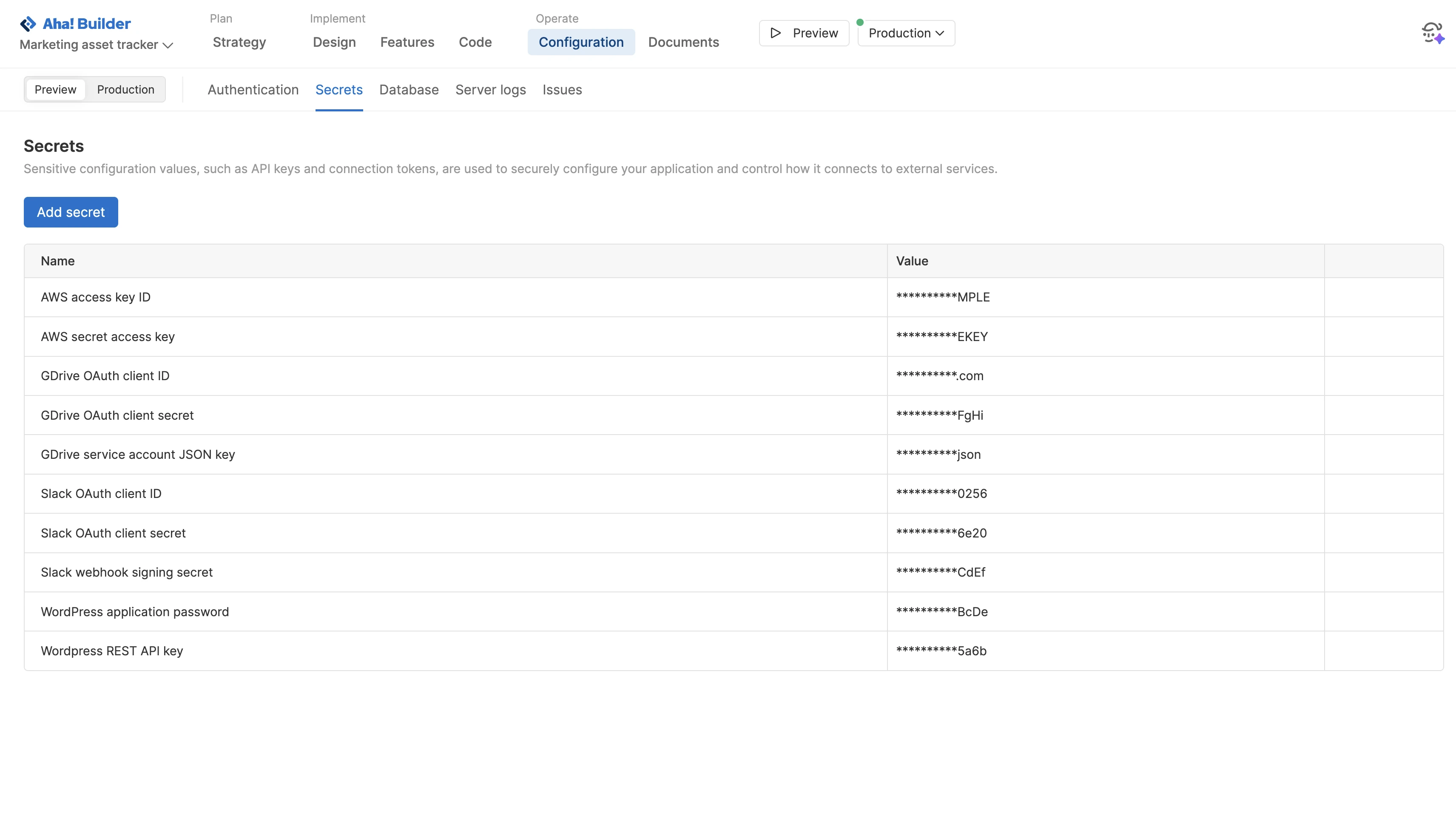
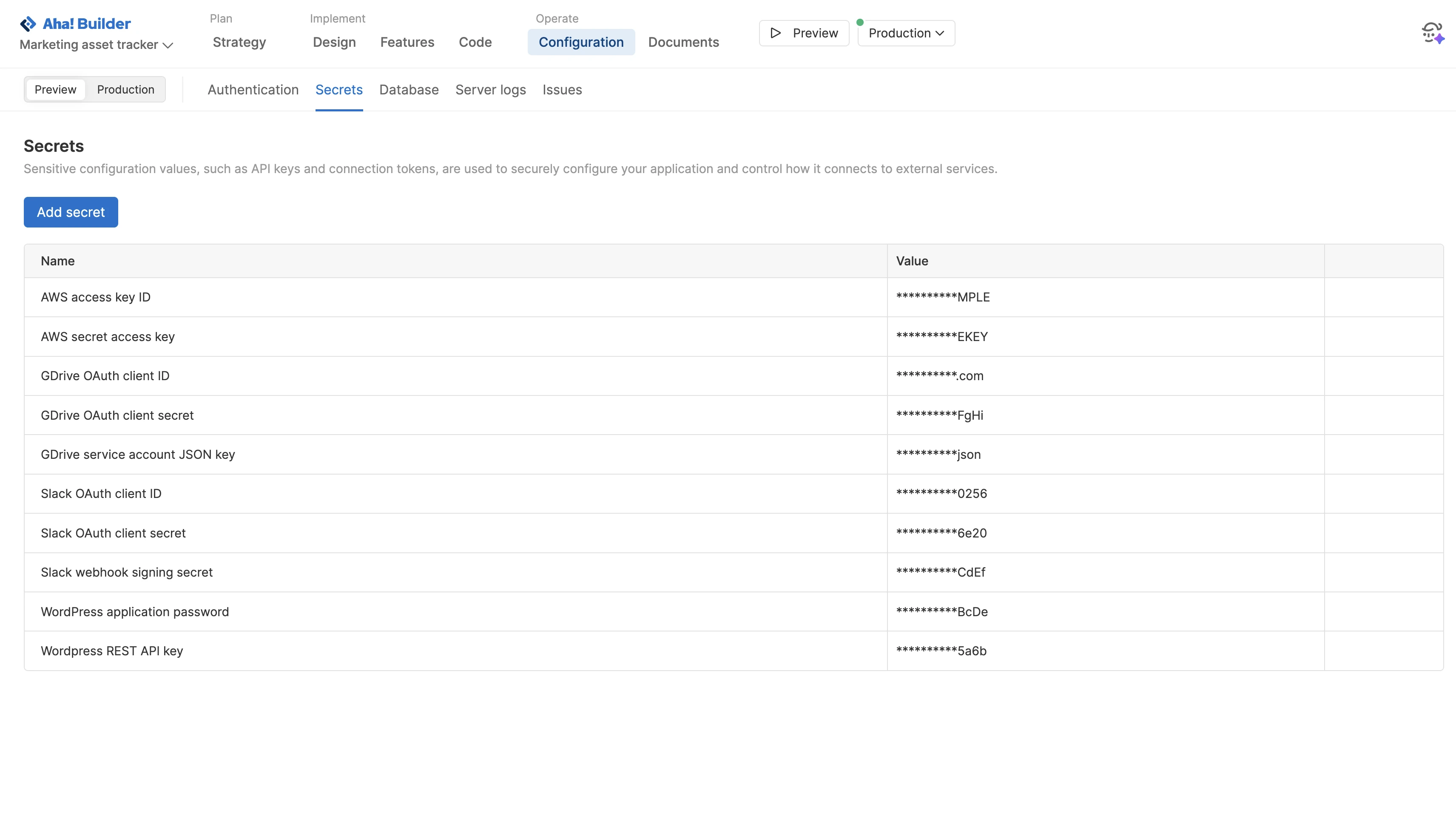
Store API keys, connection tokens, and other sensitive configuration values securely. Secrets are never hard-coded or exposed in your codebase — preventing accidental leaks and making credentials easier to manage and rotate. Reference them when setting up integrations with payment processors, messaging platforms, and data providers to establish secure, encrypted connections.
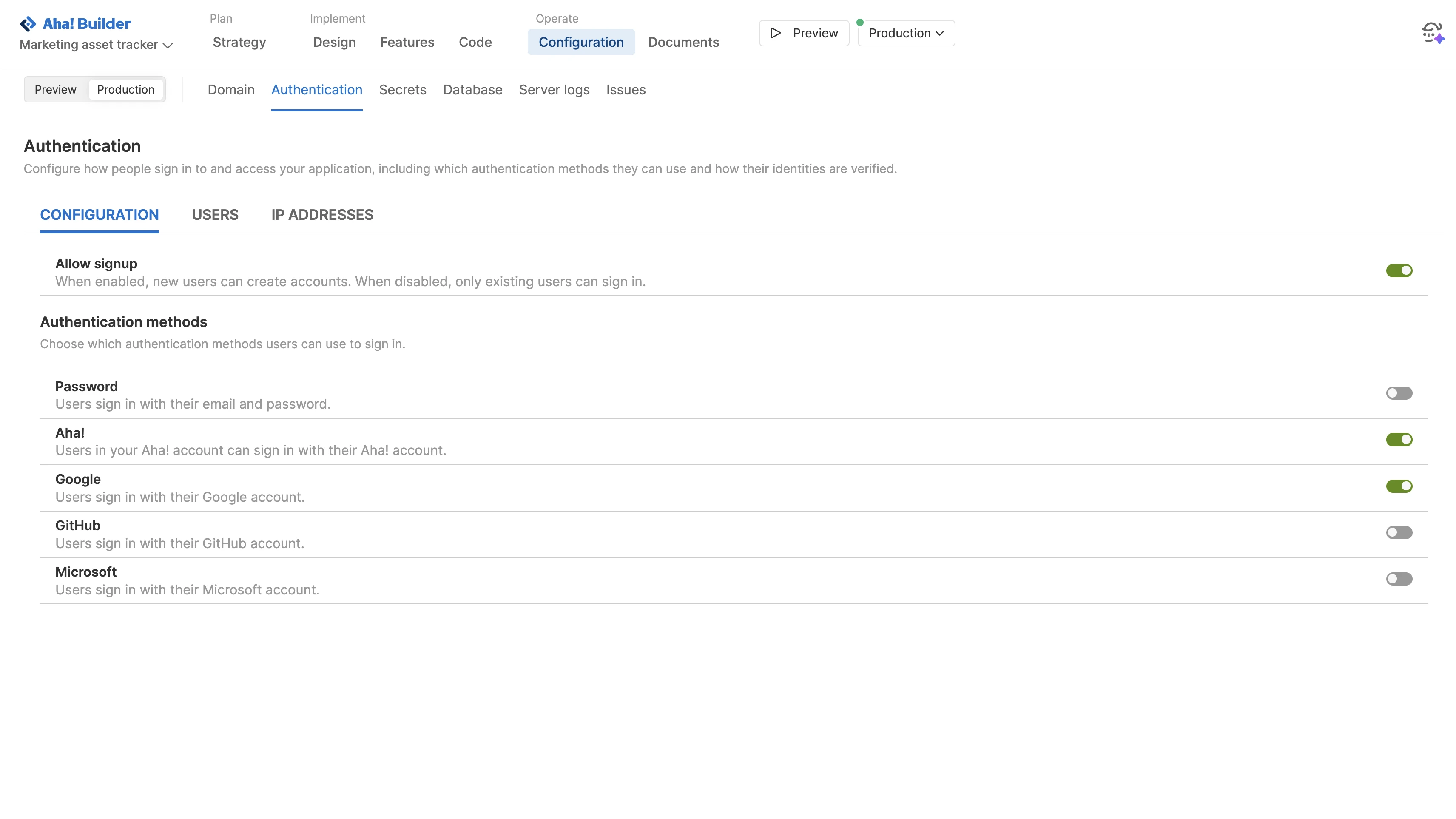
Define how people access your application. Enable signup so new users can create accounts, then choose which authentication methods to support. Options include passwords, single sign-on with your Aha! account (or Google, GitHub, or Microsoft account), or any SAML-based provider. Use one view to see who has access and how their identity is verified for complete visibility.
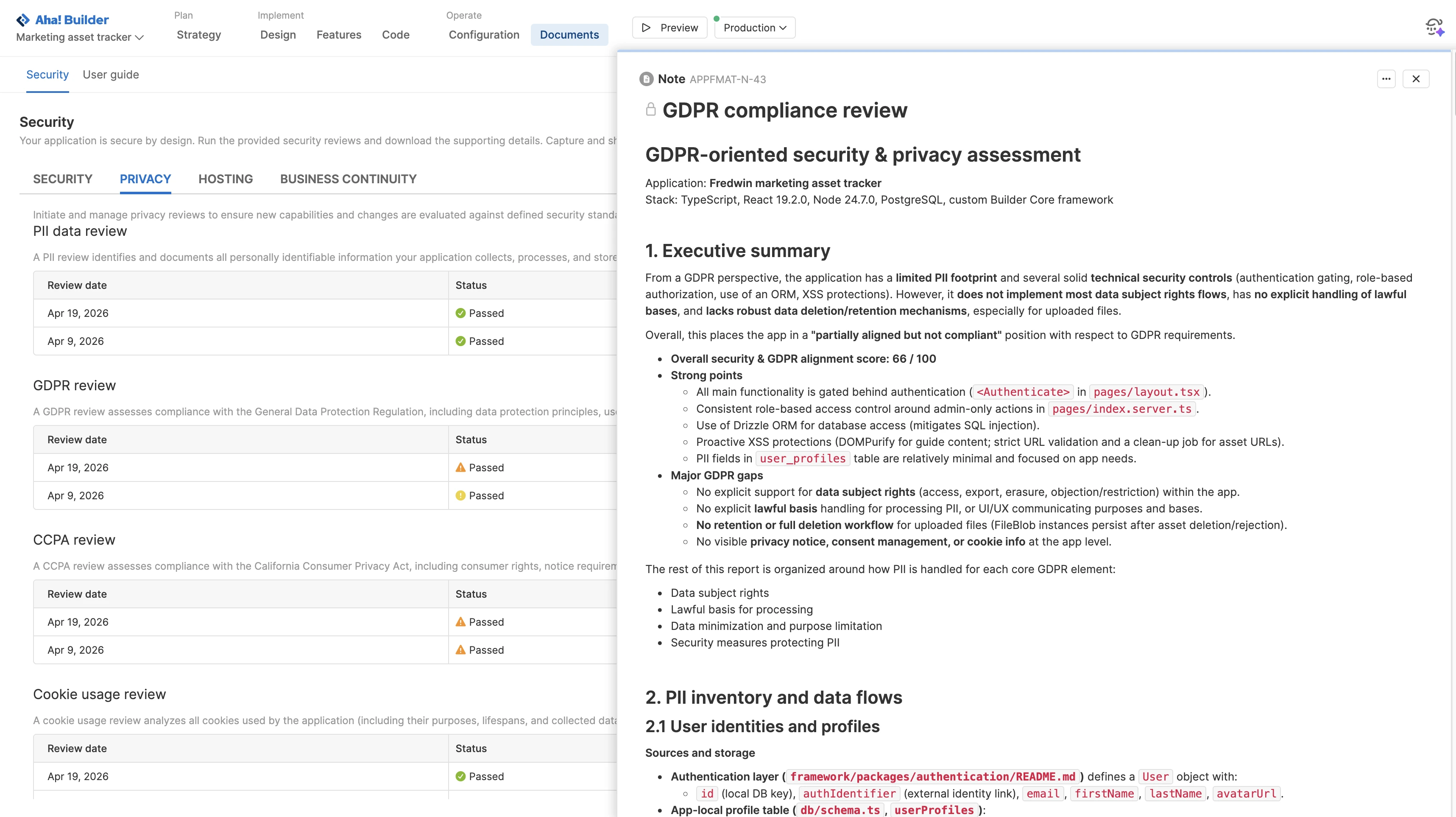
Run pre-built code and privacy reviews. Analyze your application for secure-by-design principles and conduct an OWASP assessment. Initiate privacy reviews — including PII, GDPR, CCPA, and cookie usage. Share reports with IT and compliance teams to streamline approvals and meet audit or regulatory requirements.
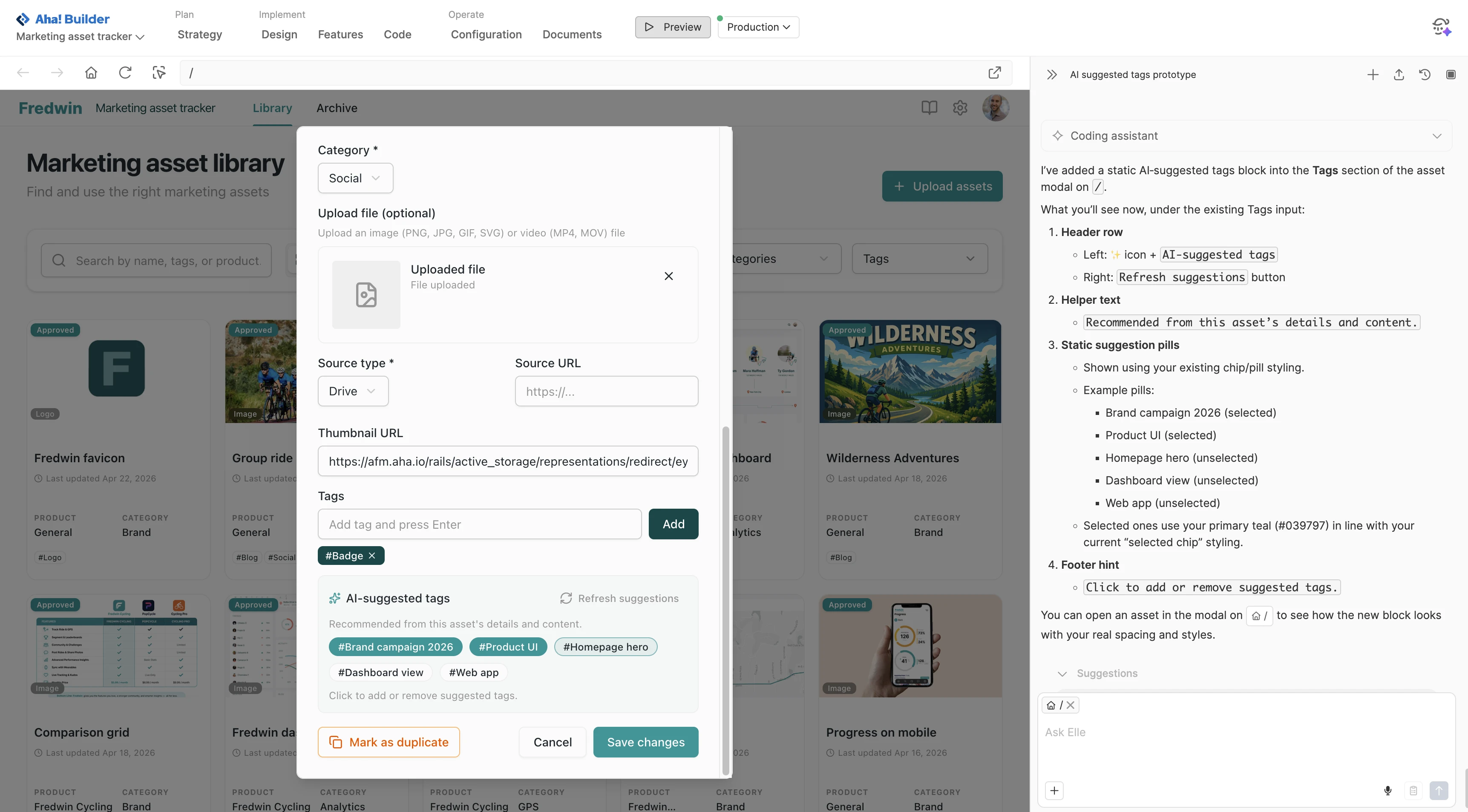
Configure common functionality — like AI services, email delivery, scheduled tasks, and background jobs — without having to build it yourself. These capabilities are ready to use, so you do not have to implement the supporting infrastructure from scratch. This reduces the risk of security gaps that come with insecure custom code, inconsistent patterns, and avoidable configuration mistakes.
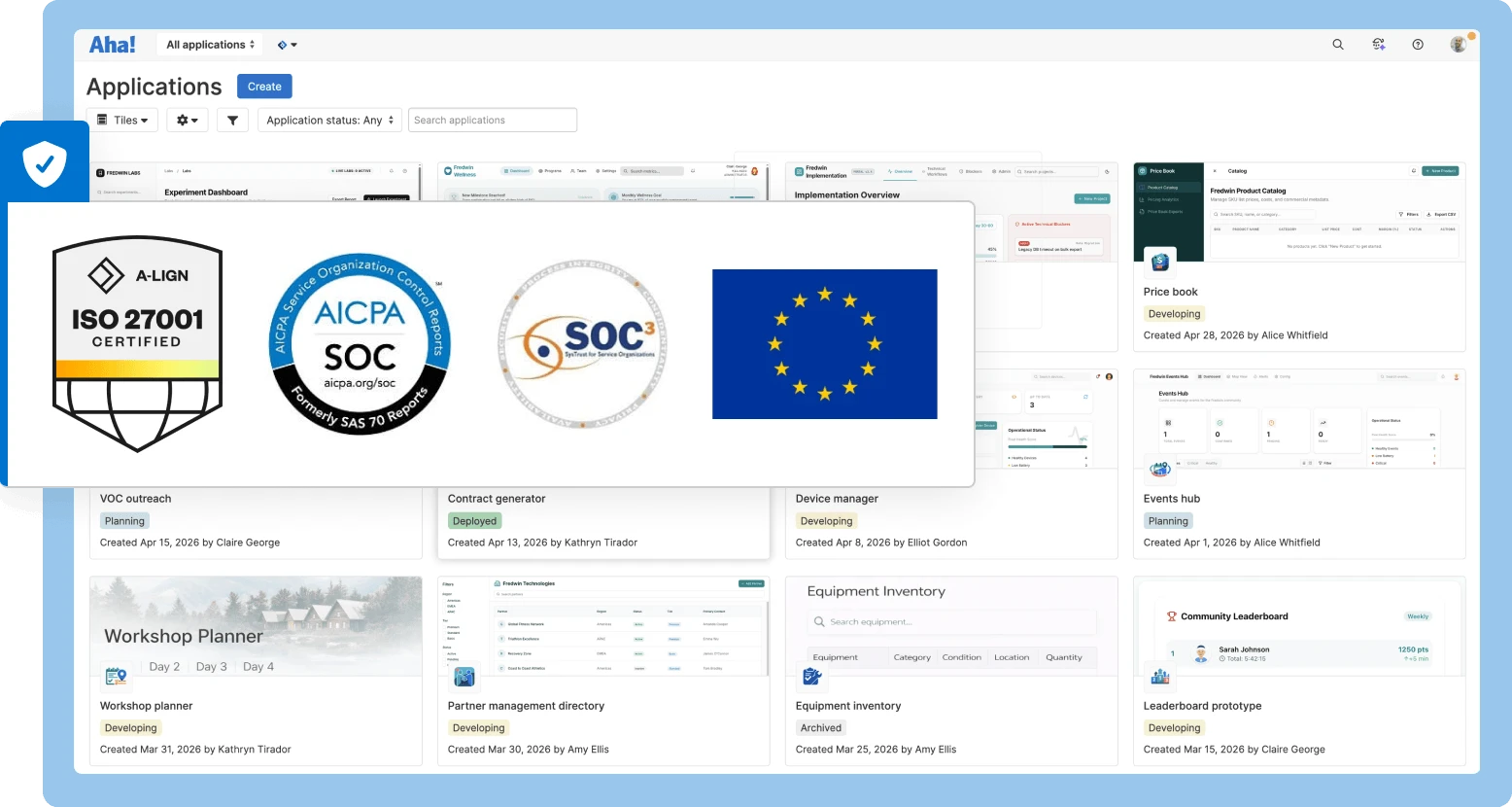
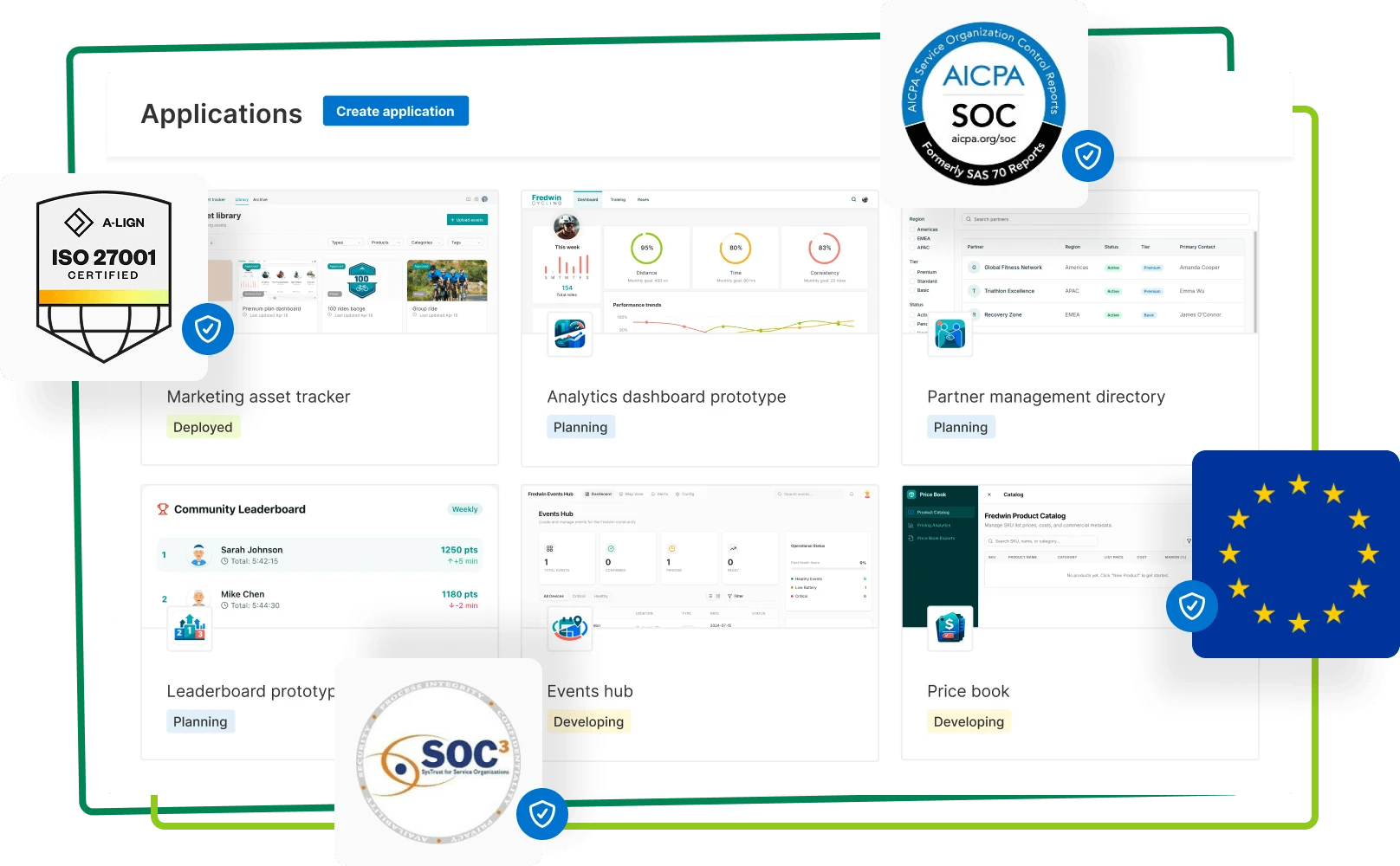
Host applications in an enterprise-grade cloud environment. Managed by Aha! and powered by AWS, you benefit from a proven platform that is ISO 27001 certified and compliant with SOC 1, 2, and 3 standards. Built-in security controls include encryption in transit and at rest, access controls, and firewalls. Move to production knowing your applications are secure, scalable, and fully supported.